Send feedback
How AlloyDB Omni uses TLS
Stay organized with collections
Save and categorize content based on your preferences.
Preview
This feature is
subject to the "Pre-GA Offerings Terms" in the General Service Terms section of the
Service Specific
Terms .
Pre-GA features are available "as is" and might have limited support.
For more information, see the
launch stage descriptions .
For information about access to this release, see the access
request page .
Select a documentation version:
18.1.0keyboard_arrow_down
AlloyDB Omni uses Transport Layer Security (TLS) to secure
communications between itself and external components such as PostgreSQL
clients, backup servers, and database applications. If you don't configure TLS
yourself, then AlloyDB Omni configures it for you using
self-signed certificates.
For more information on configuring the TLS certificates required for
AlloyDB Omni, see
Configure TLS certificates .
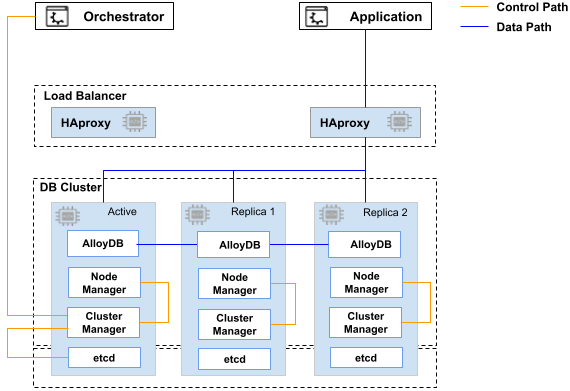
The following diagram illustrates the communication and network paths used in
AlloyDB Omni.
The following table lists each communication path and its required certificate.
Communication path
Required certificate
etcd <--> etcdetcd SSL certificate
AlloyDB Omni orchestrator <--> Cluster manager
Control path SSL certificate
Cluster manager <--> etcd
etcd SSL certificate
Cluster manager <--> Node manager
Control path SSL certificate
PostgreSQL client <--> HAProxy <--> AlloyDB Omni
Data path SSL certificate
PostgreSQL Client <--> PgBouncer <--> HAProxy <--> AlloyDB Omni
Data path SSL certificate
AlloyDB Omni <--> pgBackRest repository server
Data path SSL certificate
AlloyDB Omni <--> log server (ELK stack)
Data path SSL certificate
What's next
Send feedback
Except as otherwise noted, the content of this page is licensed under the Creative Commons Attribution 4.0 License , and code samples are licensed under the Apache 2.0 License . For details, see the Google Developers Site Policies . Java is a registered trademark of Oracle and/or its affiliates.
Last updated 2026-05-20 UTC.
Need to tell us more?
[[["Easy to understand","easyToUnderstand","thumb-up"],["Solved my problem","solvedMyProblem","thumb-up"],["Other","otherUp","thumb-up"]],[["Hard to understand","hardToUnderstand","thumb-down"],["Incorrect information or sample code","incorrectInformationOrSampleCode","thumb-down"],["Missing the information/samples I need","missingTheInformationSamplesINeed","thumb-down"],["Other","otherDown","thumb-down"]],["Last updated 2026-05-20 UTC."],[],[]]